- | Technology and Innovation Technology and Innovation
- | Data Visualizations Data Visualizations
- |
Agencies Fail 2014 Cyber Report Card and Report Record Number of IT Breaches
This weeks’ charts use data from the Office of Management and Budget’s (OMB) FY 2014 Federal Information Security Management Act (FISMA) compliance report to display the agency share, type, and number of reported federal information security incidents for FY 2014 and over time.
The recent congressional push to expand federal influence over private cybersecurity practices through controversial measures like the Cybersecurity Information Sharing Act (CISA) follows the worst year for federal information security failures on record. Many of the agencies that would be empowered to extract personal data from private entities through CISA had high rates of breaches in FY 2014. The federal government’s continuing challenges to properly secure its own systems render it a poor candidate for expanded control of the nation’s cybersecurity.
This weeks’ charts use data from the Office of Management and Budget’s (OMB) FY 2014 Federal Information Security Management Act (FISMA) compliance report to display the agency share, type, and number of reported federal information security incidents for FY 2014 and over time.
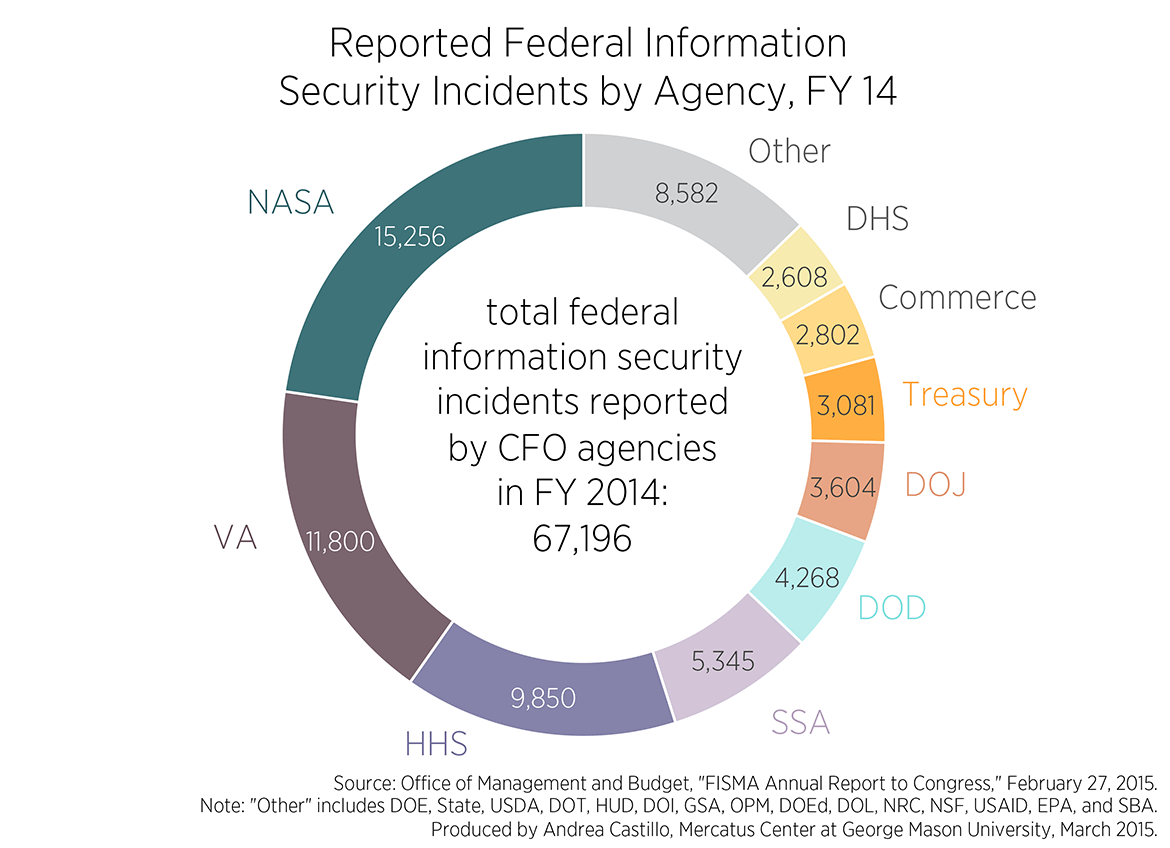
The first chart displays the total number of information security incidents reported by the 24 “CFO agencies” (so designated by the Chief Financial Officer Act of 1990) that are held to stricter FISMA standards and reporting requirements for FY 2014.
NASA accounted for 15,256 of the 67,196 information security incidents reported by CFO agencies last year, 12,017 of which are categorized as “other,” while another 1,226 malware infections and 1,185 “social engineering” incidents — where federal employees are fooled by fake webpages to download malicious software —as the second chart, below, explores in greater detail.
The Department of Veteran’s Affairs — which suffered numerous data breaches throughout the 2000s and recently ignored reports of impending cybersecurity peril only to expose personally identifiable information (PII) for thousands of veterans to outside groups — came in second with 11,800 reported incidents, 4,877 of which were non-cyber, 2,490 of which involved policy violations, 2,065 of which related to unauthorized equipment access, and 1,583 incidents of malware.
The Department of Health and Human Services — recently thrust into a much more prominent data management role through its responsibilities managing the Affordable Care Act — reported the third highest number of incidents, consisting of 3,631 non-cyber incidents, 2,000 policy violations, and 1,060 malware infections.
Importantly, the agencies that would be entrusted with significant new data extraction and management responsibilities under CISA reported alarming security breaches last year. Employees at the Department of Justice (DOJ) were fooled by deceptive websites to download malicious software onto agency computers 182 times in FY 2014. The Department of Homeland Security (DHS) reported 1,816 pieces of computer equipment lost or stolen. Department of Defense (DOD) personnel downloaded malware onto network systems 370 times and reported roughly 2,500 employee policy violations in the past year alone. These disquietingly elementary mistakes suggest that DOJ, DHS, and DOD may be ill-prepared to responsibly and effectively undertake proposed CISA authorities.
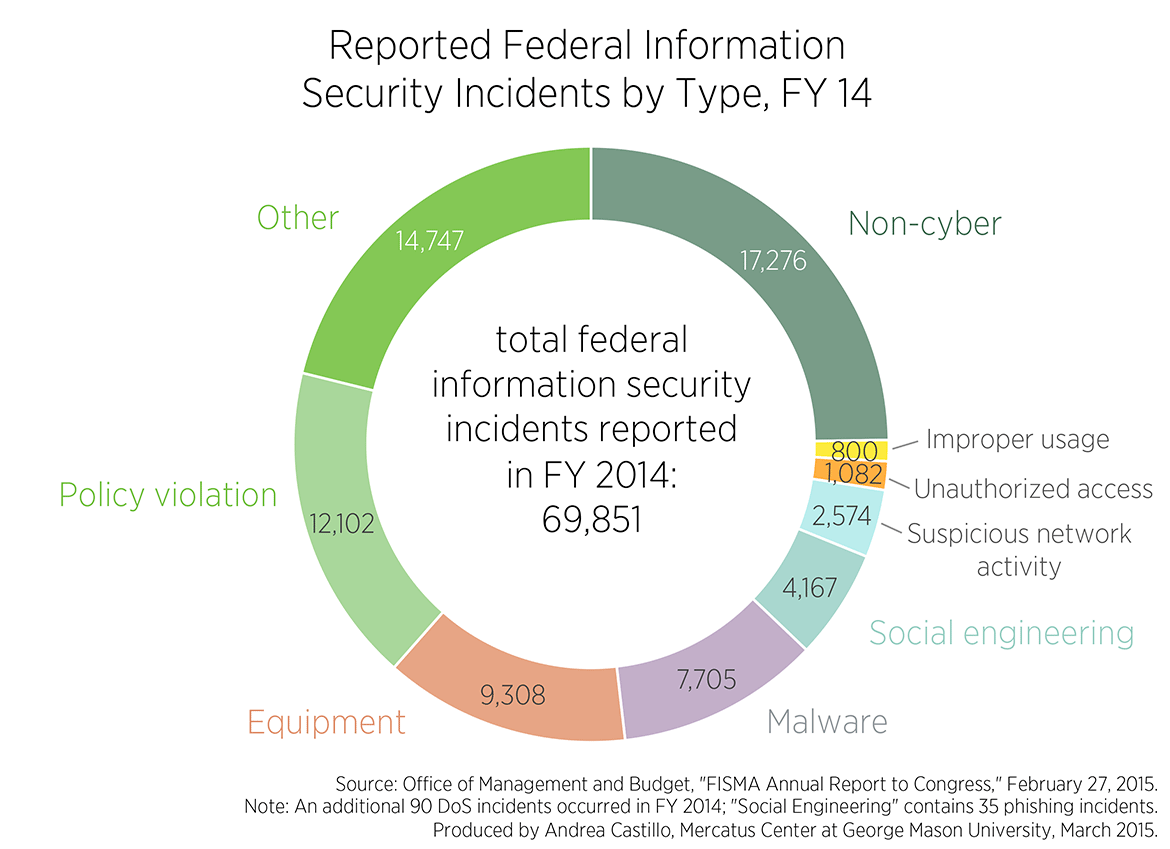
The second chart breaks down the figures by incident type. Non-cyber violations involving lost or mishandled physical records constituted the largest portion of information security incidents last year. The 14,747 incidents reported in the catch-all “other” category that includes random, miscellaneous, or unknown information breach incidents, also contributed to a large bulk of all information security failures in FY 2014.
Policy violations, where federal employees fail to follow PII management procedures, made up the third most common information security failure last year, with 12,102 reported. Lost, stolen, or otherwise missing federal equipment incidents were also high, with 9,308 reported in FY 2014. Malware is likewise known to have infected federal networks at least 7,705 times.
The report concludes that around half of last years’ incidents could have been easily avoided through the use of strong authentication techniques, which prevent unauthorized access by requiring users to log in with unique Personal Identity Verification Cards. But many agencies have made little progress in reaching internal strong authentication goals.
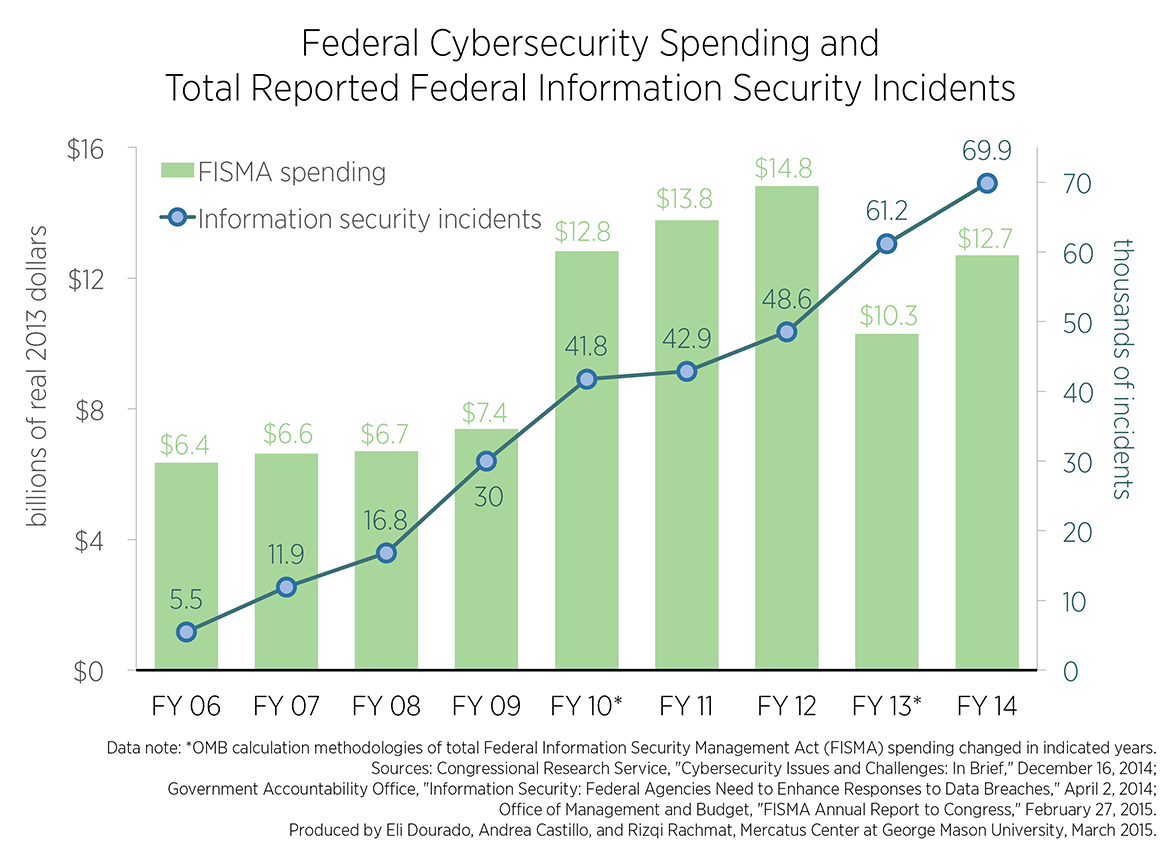
The third and fourth charts are updated versions of a previous Mercatus Center analysis from January. Total reported cybersecurity incidents reached an all-time high of almost 70,000 incidents last year. Despite spending $2.4 billion in increased FISMA spending between FY 2013 and FY 2014, the number of reported federal information security incidents increased by 15 percent—from 61,214 in FY 2013 to 69,851 in FY 2014. Since FY 2006, the total number of reported information breaches increased by an astounding 1169 percent.
Part of the rise in reported information security incidents in FY 2014 can be attributed to “enhanced capabilities to identify, detect, manage, recover and respond to these incidents” — through enhanced incident reporting requirements to US-CERT and the new EINSTEIN 3 threat detection and repulsion software of the National Cybersecurity Protection System (NCPS) — as well as an overall increase in actual incidents. Accordingly, the true number of federal information security incidents in previous years may have been even greater than initially reported.
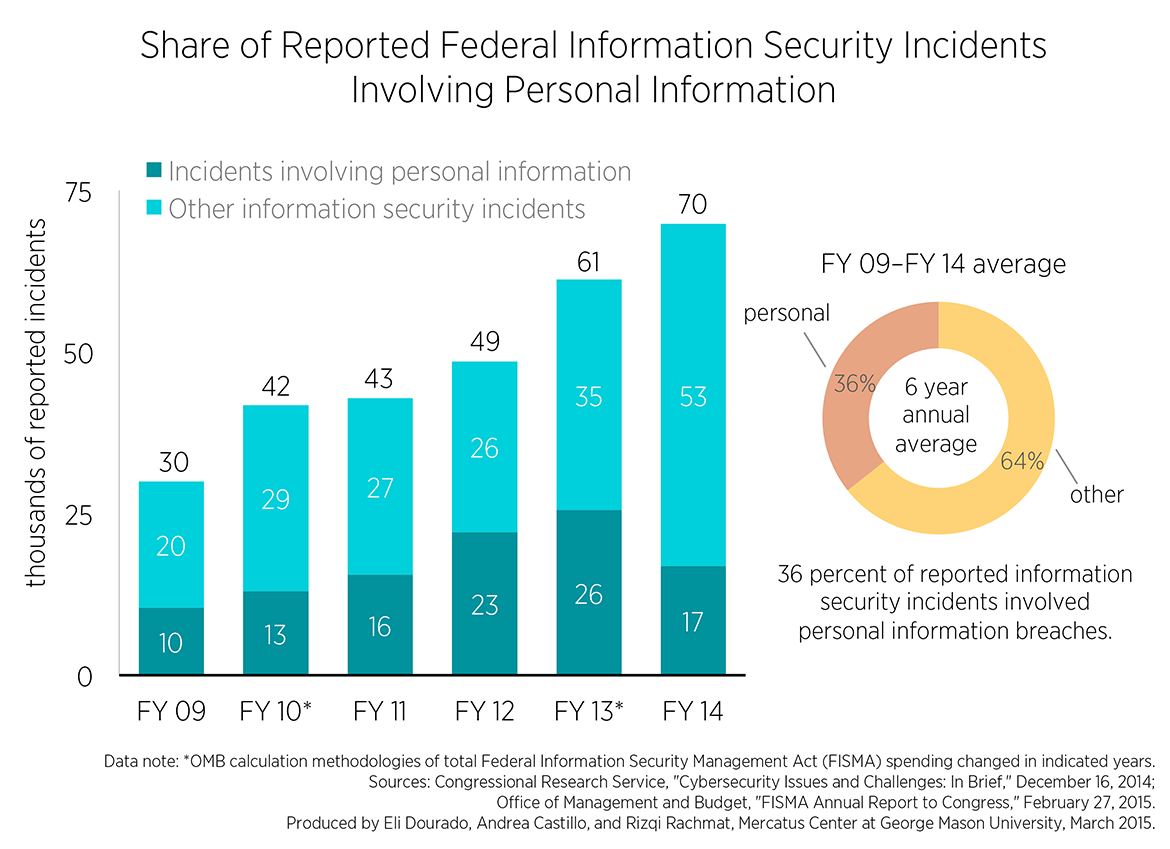
The number of reported security incidents involving PII did slightly decrease overall and as a share of the total incidents between FY 2013 and FY 2014, but this damaging type of breach still constitutes roughly a quarter of all reported incidents.
The federal government’s continuing struggles to secure its own information security systems renders it a poor candidate for exerting more control over private cybersecurity policy. Agencies that would be empowered to collect and retain massive amounts of private data, like the DOJ, DHS, and DOD, have reported hundreds to thousands of careless cybersecurity failures each year. Giving these agencies expanded authority to extract private data is unlikely to improve national computer security preparedness. Rather, private and public information security will be attained by encouraging bottom-up “notice and response” approaches to disseminate knowledge about identified cyber-breaches among appropriate parties that properly align each level of dynamic security